Email remains the number one entry point for cyberattacks, with phishing, spoofing, and business email compromise (BEC) continuing to target organizations of every size. Yet many organizations have been surprisingly slow to adopt DMARC (Domain-based Message Authentication, Reporting and Conformance), the protocol that prevents domain spoofing and protects brand trust — and one of the most effective defenses against these threats.
Businesses often have concerns about technical complexity, lack of expertise, or the impact they think DMARC might have on their legitimate email traffic. But as the risk landscape continues to evolve and more regulators, email providers, and industries put mandates in place, failing to enforce DMARC increasingly signals:
- Weak brand protection
- Higher phishing exposure
- Reduced email deliverability trust

The question is no longer “Should we implement DMARC?”. It’s “How can we implement DMARC effectively without disrupting legitimate email traffic?”.
This article explains why DMARC enforcement is becoming a priority, the common perceived challenges organizations face, and how these problems can be easily solved.
What is DMARC and why has it become a priority?
Email is the number one attack vector for phishing, spoofing, and business email compromise (BEC). DMARC builds on SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) to:
- Authenticate legitimate email senders
- Prevent domain spoofing
- Provide reporting visibility into email activity
- Allow organizations to reject or quarantine fraudulent emails
When properly enforced using quarantine or reject rules DMARC prevents phishing that impersonates your domain.
DMARC is becoming a mandatory standard for email deliverability and security
Major email providers, government agencies, and industry standards are now requiring DMARC adoption:

- Microsoft, Google and Yahoo require DMARC for organizations sending more than 5,000 emails per day
- US Federal Agencies, public sector organizations in the UK, and government agencies in Canada, Denmark, the Netherlands, and New Zealand all require mandated DMARC use
- PCI DSS v4.0 mandates DMARC for any business handling payment card data, as does DORA (EU) for financial institutions
Overcoming perceived challenges in implementing DMARC
There are three main perceived barriers to DMARC implementation, all of which can be easily addressed:
- Lack of DMARC technical/internal expertise
- Complexity and difficulty in implementing across all email sources
- Fear that legitimate email will be disrupted, impacting business
No specialist DMARC expertise is needed
DMARC depends on correct configuration of SPF records, DKIM signing, domain alignment and DNS configuration. It sounds highly technical, especially for organizations that don’t have in-house email authentication expertise or dedicated email security teams. There’s also a mistaken belief that all DMARC reporting is XML-based and difficult to interpret.
LetsDMARC resolves the ‘lack of expertise’ issue for you by providing:
- quick and easy configuration and management of your DMARC, DKIM and SPF settings through an on-screen step-by-step guide, making it simple for anyone to set up without specialist knowledge
- user-friendly dashboards that tell you all you need to know about message flow, including pass, quarantine and reject rates
- on-screen guidance through the data, together with recommendations for any actions you should take, if needed
Implementation across all email sources can be made simple
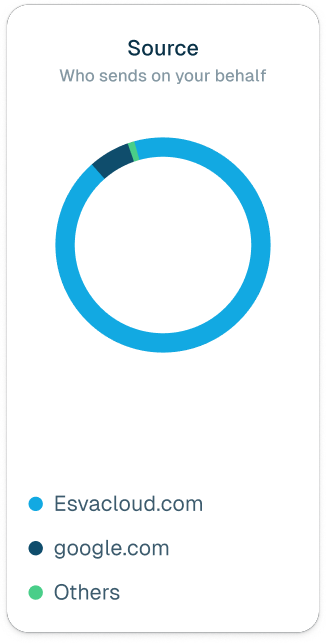
Most organizations send email from multiple services, each of which must be authenticated and aligned to avoid email delivery failures:
- CRM platforms
- Marketing automation tools
- HR systems
- Finance platforms
- Helpdesk/ticketing systems
Libraesva solves this challenge for you, as LetsDMARC will easily identify, validate, and authenticate all your valid senders.
Legitimate email sources can be validated ahead of DMARC enforcement, to avoid business risk
DMARC has three policy settings: monitoring (p=none), quarantine (p=quarantine) or reject (p=reject).
Monitoring means you’re collecting data (and in some cases this is enough to be seen as ‘compliant’) but you’re not actually blocking fraudulent emails — those that fail to pass SPF or DKIM checks — are still delivered.
Switching policy away from p=none means taking positive action by rejecting or quarantining emails, and some organizations fear that this action will:
- Block legitimate third-party senders
- Interrupt customer communications
- Impact invoices, password resets, or order confirmations
- Create reputational damage if emails bounce
However, if Libraesva LetsDMARC has authenticated, validated and aligned all your legitimate email sources, this risk is removed. Once this is complete, you can change your policy to p=reject with confidence.
Implement next-level domain protection
Cybercriminals are continually registering new domains with lookalike names or suspicious similarities to legitimate brands. Domain Guardian — a valuable feature within LetsDMARC — advances your domain protection beyond simply reacting to phishing attacks: you can stop them before they start.
Using Libraesva’s Advanced NeuroPhish AI engine, Domain Guardian identifies potential lookalikes or suspicious similarities to your own domain (sometimes called ‘typosquatting’ or ‘brandjacking’) and alerts you immediately. You can then be proactive in reporting them to domain authorities in order to protect your brand and customers from potential phishing attacks.
FAQ
What happens if you only use p=none in DMARC?
Is DMARC mandatory?
How does DMARC improve email deliverability?
What’s the problem of the SPF 10-lookup limit and how can I solve it?