In March 2026, the White House issued an Executive Order explicitly naming phishing, business email compromise (BEC), ransomware delivery, and impersonation schemes as coordinated threats warranting a federal response. It directed agencies to harden digital systems, mandate information sharing between public and private sectors, and hold foreign states accountable for harboring cybercriminal infrastructure.
That’s a clear signal to U.S. businesses that email security is more important than ever. The EU has been moving in a similar direction for much longer. NIS2, DORA, and an increasingly aggressive GDPR enforcement posture have already shifted the compliance baseline for organizations operating across borders. While they may not be planned in tandem, these efforts are global, and email is at the center of nearly every threat these frameworks are designed to address.
What Do Global Mandates Require?
For IT and security teams, the frameworks translate into specific, auditable controls. These aren’t high-level recommendations; regulators increasingly expect to see documented implementation and evidence of enforcement:
- Email authentication enforcement (SPF, DKIM, DMARC): Domain spoofing and impersonation are explicitly called out in both the U.S. EO and NIS2 as preventable attack vectors. DMARC policies at p=reject or p=quarantine, with verified DKIM signing and strict SPF alignment, are fast becoming the baseline expectation. Misconfigured or absent authentication records are low-hanging fruit for auditors and attackers alike.
- Tamper-proof archiving: Legal defensibility depends on immutable message stores. GDPR, financial services regulations, and sector-specific rules require that email records be preserved in a format that can be produced quickly and verified as unaltered in the event of e-discovery, regulatory audit, and breach investigation. That means emails must be indexed and stored in encrypted archives with access logging and retention policy enforcement, not just backup folders.
- Data residency and sovereignty controls: Under GDPR and NIS2, where your email data sits and transits matters. Cloud-native email security solutions that route traffic through third-country infrastructure may introduce compliance exposure that isn’t immediately visible. IT teams need clear visibility into which jurisdictions their mail flows through and where message stores are physically located.
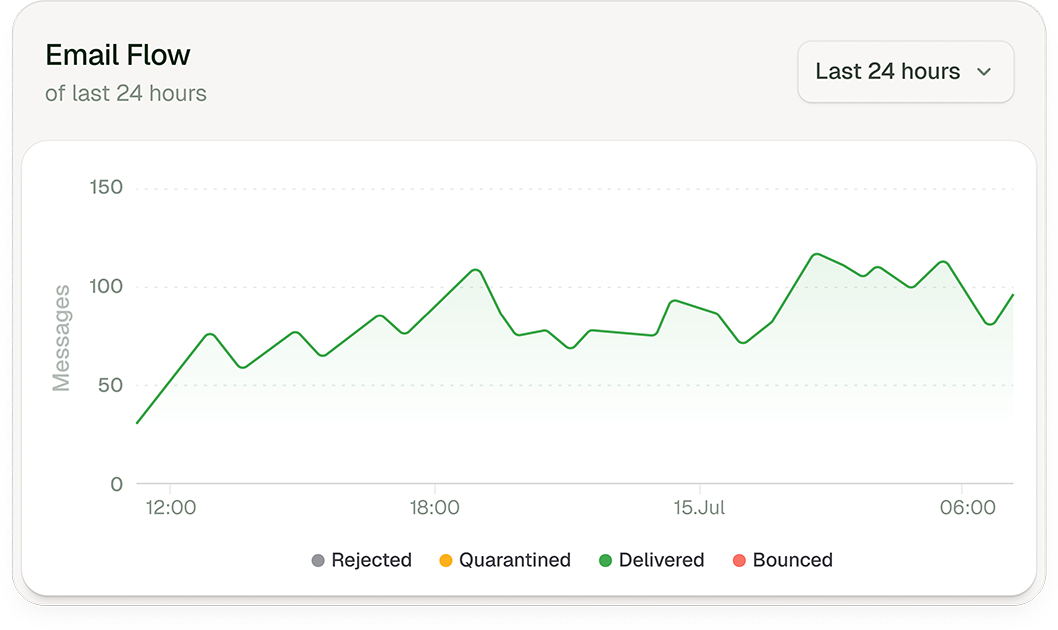
- Layered threat detection with audit trails: Advanced attachment sandboxing, URL rewriting and detonation, and real-time header analysis aren’t new concepts, but regulators now expect proof they’re in good working order. Logging and alerting configurations need to support mandatory incident reporting timelines (72 hours under GDPR and NIS2) and produce forensically useful data when an incident occurs.
- AI-powered threat detection: NIS2 Article 21 requires organizations to implement technically appropriate measures proportionate to current risk. Today, current risk includes LLM-generated phishing that passes grammar checks, mimics internal writing styles, and evades signature-based filters.
Email: Still the Highest-Risk Compliance Surface
Phishing remains the leading initial access vector in reported breaches. BEC losses run into billions annually, and ransomware payloads still arrive predominantly via email. That’s why email controls are implicitly or explicitly referenced in virtually every major framework in place or currently being drafted.
The compliance problem isn’t just about stopping the attack. It’s about demonstrating that appropriate controls were in place after the attack. This could include authentication that was enforced at the policy level, suspicious messages that were flagged and quarantined, or an archive that reconstructed the full message chain when required. Without these types of audit trails, an organization that manages to avoid a data breach can still fail a compliance review.
| The compliance problem isn’t just about stopping the attack. It’s about demonstrating that appropriate controls were in place after the attack. |
There’s also personal liability involved. NIS2 explicitly extends enforcement accountability to senior management. The U.S. SEC has moved in the same direction for public companies. Board-level exposure to enforcement action is now a real consequence of inadequate email security posture, and IT teams are increasingly being asked to brief leadership on potential exposure.
What Does Compliance-Ready Protection Look Like?
Most organizations have some email security protocols and solutions in place. The gap is usually a coherent set of solutions and a unified enforcement policy. Fragmentation is what regulators expose when they ask for an incident timeline, a data residency map, or evidence that DMARC is actually being enforced rather than just configured.
Compliance-ready email security enforces your authentication policy end-to-end, maintains an immutable encrypted archive with granular access controls and retention policies, supports data residency requirements by design, and generates the data needed to satisfy mandatory reporting timelines.
How Libraesva Can Help
Our platform is built for organizations that need to meet (and exceed) regulatory requirements, not just focus on the bare minimum.
Do you want to walk through your specific environment and compliance challenges with one of our experts?